"Don't find fault. Find a remedy."
- Henry Ford, Founder Ford Motor Company

Managed Services
When investing in business systems technology to automate your business, it's good having the assurance that important services are available from the company you selected to implement, manage, and support your systems.
Our Managed Services are designed to keep your systems secure, healthy and up to date.
We use comprehensive tools needed to secure, maintain and improve IT.
Having real-time information on system status is critical to solving small problems before they become expensive disasters. Our Health Checks and Patch Management Remote Monitoring services keeps your systems healthy and up to date.

Keep Your Environment Healthy
Real time Remote Monitoring Management (RMM) provides us complete visibility to stay on top of everything to help prevent and quickly resolve issues.
Monitor Everything
From operating systems, health checks, anti-virus, web protection, network security, to disaster recovery. Our tools allow us to monitor all critial systems.
Proactive Maintenance
Standardized Checks and Background Maintenance allows us to resolve issues without disrupting end users, while Scheduled Maintenance can run during your non business hours.
Patch Management
Allow us to keep critical systems up to date with the latest security patches to help prevent common exploits.
We provide you with secure anywhere, anytime access to your stores.
Our Take Control provides a seamless, secure remote access experience - wherever you are. One click allows quick and easy remote access from our Remote Management Dashboard - as if you were sitting right in front of the remote computer.
Secure Two-Factor Authentication
To meet PCI DSS Requirements, all remote viewing sessions occur over a secure connection and have low impact on bandwidth and requires the use of Two-Factor Authentication, such as the Google Authenticator app.
Remote Access from Multiple Devices
Using a MAC, PC or iOS device? No problem. Take Control supports Remote Access using a MAC, iOS device or standard Windows computer including support from multiple web browers.
File Transfer
Need to remote into the store to transfer files? No problem. With our Take Control, simply remote in and access the file transfer utility to quickly and securely transfer the files needed.
Simultanous Multi-User Login
Need multiple team members to log in at the same time? No problem. Our Take Control allows you and/or other of your staff to log in at the same time as needed.
Keep Users Safe and Productive While They Use the Web
Do you really know if your employees are visiting web sites they shouldn’t? Web threats have increased over the past few years. From phishing sites to drive-by downloads, the dangers have never been greater. To stay safe, you need to make sure you have advanced malware protection in place along with bandwidth monitoring, content filtering, and more. JCR Systems Remote Monitoring & Management (RMM) includes web protection that keeps your workforce safe and productive with systems that have internet access. Our Managed Web Protection goes beyond enterprise antivirus software and firewalls by setting content-filtering policies, website blacklists, time- and content-based browsing policies, and much more.
Threat Protection
Our Managed Web protection helps keep your business safe by protecting against malware, phishing, adware, botnets, and spam.
Site Whitelists / Blacklists
To help improve workforce productivity, we can set and automatically enforce browsing policies that keep users off non-work related sites like gaming and social media web sites. Want to block specific web sites? Need a business website whitelisted for access? No problem, just let us know.
Access Controls
Our Managed Web protection keeps users off sites that could cause a data breach and protect the business from the legal liability that comes with a data breach.
Reporting
We can provide detailed analytics on internet usage to help spot irregularities like unusual browsing behaviors so that appropriate action can be taken to update policies as needed.
Protect Against Known Viruses and Catch New, Hard-to-Detect Malware Threats
Our Remote Monitoring & Management's Managed Antivirus helps to keep both known and emerging malware off your pos terminals, workstations and servers. Managed Antivirus not only stays up-to-date with the latest threats using traditional signature-based protection, but also protects against new viruses using sophisticated heuristic checks and behavioral scanning. With new threats created each day, businesses protect themselves by using these proactive methods to help ensure rock-solid malware protection. And not only does our Managed Antivirus provide outstanding security, it also boasts a low rate of false positives.
Extensive Signature-Based Scanning
Our Managed Antivisus uses traditional signature-based threat detection to block known threats. Deep scans are scheduled ahead of time so you don’t disrupt employees during important productive hours.
Outstanding Performance
Our Managed Antivisus keeps scans lightweight to reduce system resource drain, while reducing the number of false positives with more accurate scanning.
Heuristic Checks
Our Managed Antivisus protect against previously unknown threats using heuristic checks, which detect new, unrecognized viruses in a sandbox environment away from a business’s core systems.
Active Protection and Behavioral Scanning
Our Managed Antivisus shuts down even the most sophisticated malware via continuous real-time monitoring, which detects programs that perform actions commonly associated with malware exploits.
Lightning-Quick Recovery Restores Business Continuity after Any Disaster
When the disaster phone call comes, how will you respond? Whether it comes from a technology failure, a natural disaster, or just user error, Our Managed Cloud Backup and Disaster Recovery tool restores business continuity fast. Our unlimited Cloud Backup Accelerator with Deep De-Duplication seamlessly integrates with today’s most popular operating systems and applications. In the event of a disaster, we recover anything faster with file level recovery as well as volumes, applications, or machines.

Data Archiving
Store Your Data for as Long as You Need and Set Variable Retention Policies. A good archive means you can retrieve critical data months or years later even if you thought it was insignificant at the time. Our Cloud Backup & Disaster Recovery's cloud-based storage is set up with a mechanism to clean data after a default retention period. However, upon request we can easily enable archiving of any backup data with a click of a button to help ensure that it stays for you as long as you need.
File Versioning
Keep Files as Long as You Need. Our Cloud Backup & Disaster Recovery stores daily backups for 28 days by default. However, we know that some important files may not be edited daily, which could leave you with just a single version of crucial files. With our Cloud Backup & Disaster Recovery, you can request a minimum number of file versions to maintain so you’re never left depending on a single backup version of an important file.
Security Focused Storage
Businesses need to keep their data secure. A single breach could cause severe deficits to the bottom line—from potential lawsuits caused by losing customers’ personal information to a loss of intellectual property that gets leaked by the attackers. Our Cloud Backup & Disaster Recovery offers multiple encryption options so we can select the level of backup security needed. With secure encryption of data in motion and at rest, we help your data remain safe in secure cloud storage.
Bare Metal Restores
Sometimes, rebuilding a system is simply out of the question. When that’s the case, you need the ability to perform bare metal restores—and you need the ability to make them happen quickly so you can get systems up and running as fast as possible. Our Cloud Backup & Disaster Recovery makes this process as smooth and painless as it can be—requiring little more than a bootable USB drive. That makes bare metal backups and restores easier and faster than ever before.
Faster Backups and Restores
Optimize Your Backups and Restores and Reduce Backup Windows with True Delta Technology. Our Cloud Backup & Disaster Recovery takes the complexity out of backups and changes recovery from an exhausting challenge to a simple reality. With Cloud Backup & Disaster Recovery your initial backup is a complete copy of all your data. After that, we use True Delta deep deduplication, which sends only new data across the network to be backed up, allowing the system to deal with the delta between the existing backup and fresh data. Backup Accelerator uses these block-level changes to reduce backup windows and improve performance. Put together, these tools help ensure you can quickly restore from backup at any time without losing data.
The best way to secure your business, lower costs and reduce risk.
Our Managed Network Security Services keeps your systems more secure while helping meet PCI DSS requirements and filling out your Self-Assessment Questionnaires. Built-in Cellular Backup saves the day in keeping your payment processing live in the event of an Internet Issue.
PCI Certified Firewall
From the world’s first PCI Level 1-Certified security service that doesn’t require a private network connection. Delivered as a subscription service, your company will be protected with the same high level of network security and management that the world’s largest corporations and banks benefit from, but without the high cost and complexity. Internet traffic is monitored and managed under strict rules and policies, ensuring your business remains secure and is meeting compliance mandates such as the PCI DSS, HIPAA and others.


Automatic Failover to LTE Cellular Backup
What happens to your ability to provide great customer service in a payment processing environment when your Internet goes down? Do you turn customers away only offering cash? Your POS system might support offline store and forward spooling mode, but any of those transactions could easily decline when the internet is back online, which results in a significant loss of revenue. Our solution comes standard with built-in automatic failover LTE cellular backup with support for Sprint and Verizon so that your live payment processing is not inturrupted. Once the ISP is back online the firewall will automatically fail back to Internet providing a seamless transition.
Tired of Turning Customers Away?
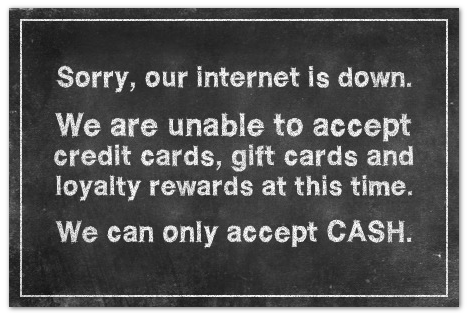
Our Automatic Failover to LTE Solution Ensures Payment Processing Continuity



Wi-Fi
The Mako features single or dual-band wi-fi and provides up to four wireless networks in one appliance. For larger coverage we offer Aerohive Wireless Infrastructure including Managed Guest Wi-Fi and Secure Wireless Point of Sale applications to fit your business needs.


Virtual Private Networks
Connected remote locations can be linked in seconds by three clicks in our Cloud Management System, all without requiring static IP addresses. For large accounts, our managed concentrators can be stacked as needed, one for every 500 store locations to provide increased performance and flexible network routing with ease.
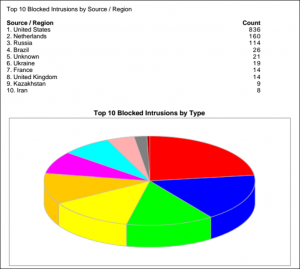
Automatic Monthly Reporting
The best part of the monthly service is having the assurance that intrusions are being prevented from penetrating your network. Using a patented communications protocal, the firewall securely sends traffic information to our Cloud Management System every few minutes. The data is used to generate graphical reports about the network, including data use by user and timeframe, intrusion attempts and network traffic. You and/or your team will automatically receive a monthly report showing report history, including the number of intrusions prevented by region around the globe.
PCI Plus - SAQ Assistance
With optional PCI Plus, we can automatically answer the PCI Self-Assessment Questionnaire (SAQ) to attest that you’re continually meeting compliance requirements.
Check Out Our Other Important Services

Professional
Services
Professional Services are available to assist through the implementation process.

Technical
Services
Technical Services are available to assist when something happens.